Juniper Networks Security Director
Extensive Security Policy Management

Click here to jump to more pricing!
Overview:
Security Director enables organizations to manage security anywhere and everywhere, on-premises and in the cloud with unified policy management that follows users, devices, and applications wherever they go. Policies can be created once and applied everywhere. Use Security Director Cloud for network-wide visibility and policy management for deployments on-premises, in the cloud, and as a service.
Security Director is the Juniper portal to a secure access service edge (SASE) architecture. Easily manage and deploy security policies from a single UI across all environments. Automate threat remediation and micro-segmentation policies across the entire network with Policy Enforcer, Security Director’s built-in security orchestration.
Key Features
- Manage tens of thousands of sites simultaneously
- Create policies for validated threat prevention, user and application access control, secure connectivity, and more — and apply them anywhere
- Protect private and public cloud workloads with metadata-based security controls
- Correlate and analyze each stage of an attack in sequence, regardless of which product made the detection, and stop threats across your network with Policy Enforcer’s one-click mitigation
- Security Assurance guarantees that security rules are always placed correctly for intended effectiveness
Features
Security Director Cloud
Security Director Cloud is your portal to Secure Access Service Edge (SASE), bridging your current security deployments with your SASE rollout. Security Director Cloud enables organizations to manage security anywhere and everywhere, on-premises, in the cloud, and as a service with unified policy management that follows users, devices, and applications wherever they go. Policies can be created once and applied everywhere. Organizations can use Security Director Cloud for network-wide visibility and policy management for deployments simultaneously to securely transition to a SASE architecture.
With Security Director Cloud, organizations can transition to a SASE architecture seamlessly, securely, and at a pace that’s best for each individual business. The bidirectional sync between Security Director and on-premises and individual firewalls, provides a cohesive management experience that supports a seamless transition to the cloud. Its unified policy management provides easy-to-use, consistent security policy that follows the user, device, and application—without needing to copy over or recreate rule sets.

The Security Director dashboard provides customizable, information-rich widgets offering visually intuitive displays that report security device status at a glance. A pallet allows you to easily navigate between firewall, threat, intrusion prevention system (IPS), application, throughput, and device-related information to create a customized view of the SRX Series firewall environment.
Security Director Insights
Security Director Insights expands end-to-end visibility by correlating and scoring threat events across the complete security stack. It offers a timeline view mapped to the MITRE attack framework, so administrators can focus on the highest priority threats. It unifies visibility across the network by correlating threat detection information, including detections from other vendor products, and it enables one-touch mitigation to quickly address gaps in defense.
Security Director Insights empowers organizations to automate threat remediation and microsegmentation policies across the entire network with Policy Enforcer, Security Director’s built-in orchestration.
With Security Director Insights, customers can:
- Understand when and where an attack is happening by using it to correlate and prioritize security events from multiple security solutions across various parts of the network.
- Use custom threat and incident scoring so that security teams respond to and can mitigate attacks that have the potential to do the most harm to the business.
- Mitigate active threats across the network—on Juniper SRX Series firewalls, EX and QFX Series switches, wired and wireless access points driven by Mist AI, along with third-party solutions—with one click.
Policy Enforcer
Policy Enforcer provides a simplified user intent-based threat management policy modification and distribution tool. It allows updated policies to deploy on Juniper Networks EX Series Ethernet Switches, MX routers, QFX Series switches, and Juniper physical, virtual, and containerized SRX Series Services Gateways.
Security Director provides automated enforcement and policy orchestration that allows updated security policies to deploy across Juniper SRX firewalls, EX Series switches, QFX series switches, MX series routers, and third-party network devices. The software helps automate threat remediation and microsegmentation policies across your entire network.
Specifications:
| Features | Description | Benefits |
|---|---|---|
| Secure Edge | Provides FWaaS in a single-stack software architecture with application control, IPS, anti-malware, web proxy and filtering, and advanced threat protection all delivered as a service. | Enables administrators to seamlessly secure their remote workforce with consistent security policies that follow the user wherever they go. |
| Security Director Insights | Collects and automatically correlates data across multiple security layers—email, endpoint, server, cloud workloads and network—so threats are detected faster, and security teams can improve investigation and response times. Prevents future attacks with mitigation rules. |
|
| Policy Enforcer | Creates and centrally manages security policies through a user intent-based system, evaluating threat intelligence from multiple sources while dynamically enforcing policies in near real-time across the network. Enforces threat management policies at firewalls and access switches, aggregating threat feeds from Advanced Threat Prevention Cloud, SecIntel, and on-premises custom threat intelligence solutions with allow list and blocklist support. |
|
| Firewall policy analysis | Provides the ability to schedule reports that show shadow or redundant firewall rules are and recommends actions to fix all reported issues. | Allows administrators to maintain an efficient firewall rule base by quickly identifying ineffective and unnecessary rules. |
| Firewall rule placement guidance | Upon creation of a new rule, analyzes existing firewall rule base to recommend optimal position and application. | Significantly reduces shadowing rules. |
| Metadata-based policies | Enables administrators to create object metadata-based user-intent firewall policies. | Simplifies policy creation and maintenance workflows. In addition to making policies more readable from a user intent perspective, this feature streamlines firewall troubleshooting. |
| Dynamic policy actions | Enables security administrators to initiate different actions, including firewall, logging, IPS, URL filtering, and Antivirus, among others, under different conditions. | Reduces the time required to adjust the organization’s security posture under different conditions and streamlines threat remediation workflows. |
| Firewall policy hit count | Shows hit counts for each firewall via meters and filters that display which rules are hit the least. Security Director also can keep a lifetime hit count. | Allows administrators to assess each firewall rule’s effectiveness and quickly identify unused rules, resulting in a better-managed firewall environment. |
| Live threat map | Displays where threats are originating in near real-time and allows you to take action to stop them. | Provides near-real-time insight into network-related threats. Allows you to block traffic going to or coming from a specific country with a single click. |
| Security Assurance | Automate security policies across the network, including firewalls, routers, and switches for accurate enforcement, consistent security, and compliance. | Guarantee that security rules are always placed correctly for intended effectiveness. |
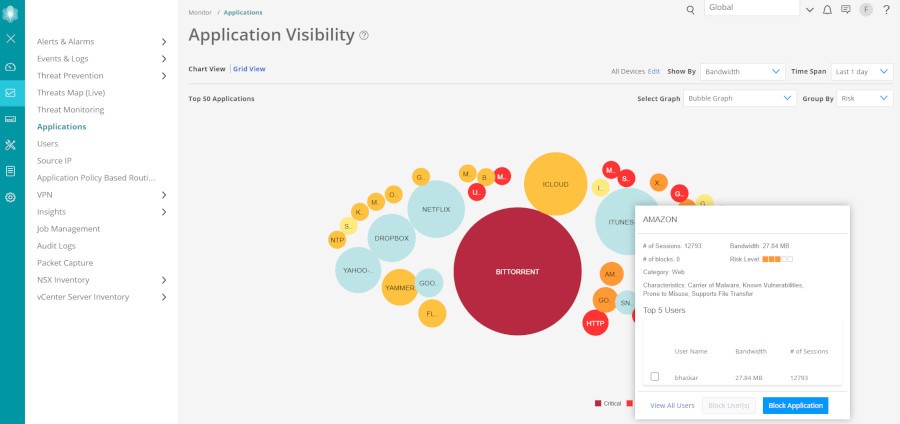
| Innovative application visibility and management | Provides an easy and intuitive way to see which applications use the most bandwidth, have the most sessions, or are most at risk. Know which users are accessing non-productive applications and by how much. Top talkers are displayed in an easy-to-understand manner. Block applications, IP address, and users with a simple mouse click. | Delivers greater visibility, enforcement, control, and protection over the network. |
| Simplified threat management | Reports where threats are originating and where they are going via a global map. Blocking a country is easy; simply mouse over the country to take action. | Provides insight needed to manage network-related threats effectively. Allows you to block traffic going to or coming from a specific country with a single click. |
| Snapshot support | Allows users to snapshot, compare, and roll back configuration versions. | Simplifies configuration changes and allows recovery from configuration errors. |
| Policy lifecycle management | Provides the ability to manage all phases of security policy lifecycles, including creating, deploying, monitoring, remediation, and maintenance. |
|
| Drag-and-drop | Allows firewall, IPS, and NAT rules to be reordered by simply dragging them to a new location. | Enables firewall, IPS, and NAT objects to be added or copied by dragging them from one cell to another or from a pallet located at the bottom of the policy table. |
| VPN auto-provisioning and import | Simply tell Security Director which VPN topology to use and which devices you want to participate in the topology, and Security Director will auto-provision the tunnels. If you have an existing Juniper VPN environment, Security Director can import the VPNs to provide an easy and effective way to manage them. | Makes pre-existing SRX Series firewall VPNs easier to manage. |
| Role-based access for policies and objects | Allows devices, policies, and objects to be placed within domains and assigns read/write permissions to a user. | Provides customers a way to segment administrative responsibility for policies and objects. |
| REST APIs for automation | Provides RESTful APIs used in conjunction with automation tools. | Automates configuration and management of physical, virtual, or containerized SRX Series firewalls. |
| Logging and reporting through Junos Space Log Director application | Enables integrated logging and reporting. |
Tight coupling with Security Director:
Direct access to Security Director policies and objects:
System log forwarding to security information and event management (SIEM) |
Documentation:
Download the Juniper Networks Security Director Data Sheet (PDF).
Pricing Notes:
- Pricing and product availability subject to change without notice.
